Aspinity has introduced a suite of new analogML™ algorithms tailored for parked-vehicle monitoring. These algorithms enable continuous vehicle monitoring without compromising battery life, addressing a critical challenge faced by the automotive industry. Additionally, the company has unveiled a dashcam-focused evaluation kit designed to enable precise detection and recording of security events over extended periods without […]
Security
Root-of-trust devices accelerate secure manufacturing and deployment
Microchip Technology is helping make embedded security solutions more accessible with its CEC1736 TrustFLEX devices. The CEC1736 Trust Shield family is a microcontroller-based platform root of trust solution enabling cyber resiliency for data centers, telecom, networking, embedded computing, and industrial applications. Now, as part of the TrustFLEX platform, the devices are partially configured and provisioned with Microchip-signed […]
Next-gen wireless chips set to meet upcoming cyber-protection standards
STMicroelectronics has revealed the next generation of its short-range wireless microcontrollers. These innovative, all-in-one components enable wearables and smart objects including smart home devices, health monitors, and smart appliances to become ever more miniaturized, easy to use, secure, and affordable. Short-range wireless technologies like Bluetooth LE, Zigbee and Thread (popular in smart meters and smart […]
Wireless SoC features low power consumption and enhanced security features
Sony Semiconductor Israel announced that its advanced ALT1350 Wireless System on Chip (SoC) is now commercially available. LPWA cellular modules have been designed by our partners and industry leaders AM Telecom, Fibocom, Murata, Quectel, Semtech, Telit Cinterion, and Wistron NeWeb Corporation (WNC). The modules are now available for sampling, with mass production expected during the […]
Securing devices for the IoT — managing memory
Memory management is important in all digital electronic devices including devices designed for use on the Internet of Things (IoT). It supports efficient resource allocation and memory utilization and prevents memory fragmentation, improving efficiency. It also supports memory protection and device security. This FAQ briefly reviews the common weakness enumeration (CWE) scheme for identifying software […]
Securing devices for the IoT — minimize the attack surface
An attack surface is the sum of all the attack vectors or ways that an attacker can gain malicious access to a network or system. The growth in remote work and the adoption of cloud services have increased the number of attack vectors and the size of the attack surface for most organizations and applications. […]
Securing devices for the IoT – FIPS 140-3 and common criteria
For developers of IoT devices and networks, the Federal Information Processing Standard (FIPS) 140-3 and the Common Criteria (CC) serve different but complementary functions. FIPS 140-3 is designed for validating software and hardware in cryptographic modules, while CC is designed to evaluate security functions in IT software and hardware. In both cases, there are related […]
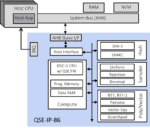
IP engine integrated into RoT or embedded secure element in SoCs and FPGAs
Rambus Inc. announced the availability of a Quantum Safe Engine (QSE) for integration into hardware security elements in ASICs, SoCs, and FPGAs. Quantum computers will enable adversaries to break current asymmetric encryption, placing important data and assets at risk. The Rambus QSE IP core uses NIST-selected quantum-resistant algorithms to protect valuable data centers and government hardware […]
Hardware-based RoT enables auto devices to meet automotive functional safety standard
Intrinsic ID released QuiddiKey 400, a hardware-based root-of-trust (RoT) solution for semiconductors in the automotive market that must meet stringent functional safety standards. QuiddiKey 400 has been developed following an ISO 26262 functional-safety-compliant flow and meets the ISO 26262 Automotive Safety Integrity Level (ASIL) B fault metric and ASIL D for systematics failures. It leverages […]
Security IC supports key sizes up to ECC P521, SHA512, RSA-4K, and AES256
As vehicles become more connected and technologically advanced, the need for heightened security measures also rises. New government and automotive OEM cybersecurity requirements are beginning to include larger key sizes and Edwards Curve ed25519 algorithm standards. In response, Microchip Technology has launched its latest TrustAnchor Security IC, the TA101, which can accommodate complex automotive and embedded security use […]