ADLINK Technology Inc. introduces the world’s first 12th Gen Intel Core processor-based Computer-on-Modules (COMs), available in two form factors – COM-HPC Client Type and COM Express Type 6. ADLINK COMs with the Intel 12th Gen Intel Core processor family (Codename: Alder Lake-H) allows for a unique design that can be adapted for single-thread or multithread performance. The […]
Security
Security development tools work on STM32 MPUs
IAR Systems presented their Compliance Suite for STM32. Compliance Suite provides developers and organizations with the security development tools, practical guidance, and knowledge needed to rapidly build applications that are compliant with security legislation, such as the US Cyber Security Improvement Act, the European Consumer IoT Security Standard EN 303 645 (ETSI), UK & Australian […]
Security technology built into MIL-STD-1553 interface
Abaco Systems announced the release of 1553Guard, a new security technology for MIL-STD-1553-based systems which provides an additional layer of protection against cyber-attacks. 1553Guard is an integrated solution which is directly built into the 1553 interface. Other technologies require expensive hardware and significant software modification but may not include threat mitigation. Abaco’s “plug-and-play” device detects […]
Module speeds security integration of OpenVPX MOSA-based systems
Curtiss-Wright’s Defense Solutions has introduced the industry’s first plug-in module to bring commercial-off-the-shelf, defense-grade system security to rugged OpenVPX-based systems. The XMC-528 Xilinx Ultrascale+ MPSoC XMC Mezzanine Card is the first member of Curtiss-Wright’s new family of enhanced TrustedCOTS (eTCOTS) solutions. This XMC (VITA 42/61) module speeds the integration of advanced security IP, such as Raytheon’s Night Cover product […]
Cloud service automates IoT device connection/registration via X.509 device certificates
Infineon Technologies AG launched CIRRENT Cloud ID, a service that automates cloud certificate provisioning and IoT device-to-cloud authentication. The easy-to-use service extends the chain of trust and makes tasks easier and more secure from chip-to-cloud while lowering companies’ total cost of ownership. Cloud ID is ideal for cloud-connected product companies in the industrial, consumer, healthcare, […]
SSDs add cybersecurity software
DIGISTOR announced its Series C secure SSDs, the first DIGISTOR SSDs to add Cigent D3E cybersecurity software. The new SSDs broaden the company’s comprehensive solutions and virtually eliminate the barrier to securing DAR with military-grade encryption for hardware and software. The company is debuting the C Series in the Trenton Systems booth (#2065) at the […]
RS-485/422 transceiver ICs feature industry-leading ±5,000-V EFT immunity
Renesas Electronics Corporation introduced the RAA78815x Family of 5V differential RS-485/422 transceivers with industry-leading electrical fast transient (EFT) immunity – ±5000V – and ESD protection up to ±16,000V, making these products the ideal solution for noise-sensitive industrial communication networks. The six new full and half-duplex ruggedized devices meet both the RS-485 and RS-422 communication standards […]
Defense in depth: What does it mean, and what can it achieve?
By Mark Pitchford, technical specialist, LDRA Connectivity has brought positive changes to embedded applications through new opportunities for easier monitoring, upgrades, and enhancements. On the downside, connected systems present more attack surfaces, which make systems vulnerable to bad actors. Defending against such attacks is a daunting task, even for organizations well versed in functional safety. […]
Security module handles V2X telematics
To provide the highest level of protection, Infineon Technologies AG is launching the SLS37 V2X hardware security module (HSM), a plug-and-play security solution for vehicle-to-everything communication (V2X). The SLS37 V2X HSM is based on a highly secured, tamper-resistant microcontroller tailored to the security needs in V2X applications within telematics control units. It is protecting the […]
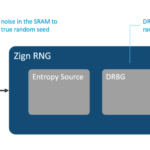
Random number generator software targets IoT devices
Intrinsic ID announced Zign RNG, a new offering enabling IoT chip providers and device makers to establish a high-security random number generator in software enabling it to be deployed on devices even after silicon fabrication to ensure a true source of randomness for IoT devices. Random number generators (RNGs) are essential for cryptographic applications and form […]