Demands for bandwidth-intensive, data-driven services are fueling a rise in compute, data storage, and networking capabilities. These rises put pressure on connectors and cable to deliver data at higher speeds with better signals and less heat.
Featured
Sorting out balanced cables and differential signaling
Lines carrying symmetric signals, i.e. those with opposite polarities but with equal amplitudes on each line are commonly called balanced. But the correct term is differential signaling. While balanced lines and differential signaling may be used together, they are actually quite different. The key point that distinguished balanced lines from single-ended lines is that both […]
What materials can be used to make miniature antennas?
Many antennas are mechanically simple and electrically complex at the same time. Mechanically an antenna usually has only one or two components, a dielectric layer (which can be the entire antenna) and a conductive layer. This FAQ begins with a brief review of dielectric materials and their importance to antenna performance. It then explores developments […]
Will internal IO copper cables for data centers become standardized?
Data-center passive DAC external cables have been standardized and interoperable for decades. However, the mating, inside-the-box cables have yet to be fully standardized. In general, inside-the-box IO interface interconnections have been a competitive value point for those OEMs and suppliers that offer quality options. Providing reliable connectors and twin-axial cables configured in an ideal layout […]
Metrics: Figures of merit evolve to match technology, Part 2
As technology advances, new parameters and measures are necessary while some older ones fade in importance. Back in the day, there were sophisticated, detailed papers created at telecom companies and labs—such as the venerable Bell Telephone Laboratories (Bell Labs)—which analyzed the many voice-phone traffic patterns and situations, and resources needed (local loops, line interface units, […]
Enabling a do-it-yourself hot-swap circuit design using a hybrid architecture
By Durga Praveen G and Rakesh Panguloori, Texas Instruments There is unprecedented demand for highly available and redundant systems to offer the best user experience. For example, in communications, banking, and industrial automated systems, any amount of system downtime could potentially lead to lost customers. The implementation of a hot-swap circuit at the input of […]
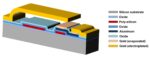
What can you make with MEMS technology?
Microelectromechanical systems (MEMS) has several names, including micro-electro-mechanical systems, and micromechatronic systems. In Japan, MEMS is called micromachines, while in Europe, it’s referred to as microsystem technology (MST). Whatever name that’s used, MEMS devices are made using components measuring from 1 to 100 μm (0.001 to 0.1 mm), with MEMS devices ranging from 20 μm […]
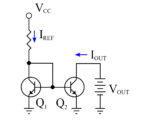
How do you use a current mirror?
Current mirrors are common circuits but are mostly invisible, except to designers of analog or mixed-signal integrated circuits who can use large numbers of current mirrors on a single chip. A current mirror copies a current through one active device (such as a BJT or MOSFET) by controlling the current in another active device. If […]
Metrics: Figures of merit evolve to match technology, Part 1
As technology advances, new parameters and measures are necessary while some older ones fade in importance. Engineering depends on metrology, measurements, metrics, and figures of merit (FOM). These allow designers to quantify performance and compare it to previous implementations and alternative designs. These factors are critical to the many essential quantitative assessments, as well as […]
Securing automotive ICs with formal methods
Best practices for protecting vehicles from hackers now include advanced verification techniques. John Hallman, David Landoll, Siemens EDA It’s no secret that much of the control for modern vehicles takes place via ICs, and any access to them may give an outsider uninvited control of the car. It is a challenge to identify the security […]