STMicroelectronics has launched STPay-Mobile, a platform that simplifies the virtualization of security-critical public transit ticketing and payment cards on smartphones and wearables. STPay-Mobile helps mobile-device manufacturers leverage the features of ST’s ST54 secure System-on-Chip (SoC) to handle contactless transactions and protect sensitive information, such as data and authentication credentials. Highlighting the value STPay-Mobile adds to card […]
Software
What is precoding and what are the benefits?
Precoding involves preprocessing of the transmit signal in an RF system. As described below, precoding uses channel state information at the transmitter to improve performance and increase spectral efficiency. It is used to implement the superposition of multiple beams, including several different data streams of information for spatial multiplexing. Precoding is the transmitter signal processing […]
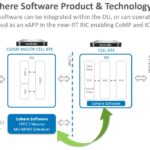
Software predicts changes in wireless channels
Spectrum Multiplier software from Cohere Technologies uses Delay-Doppler effects to predict how a wireless channel will change in real time, letting base stations control MU-MIMO beams.
Development platform meets new vehicle architecture demands
NXP Semiconductors has announced BlueBox 3.0, a new and expanded version of NXP’s flagship safe Automotive High-Performance Compute (AHPC) development platform. Designed for software application development and validation ahead of silicon device availability, BlueBox 3.0 now offers a flexible way to address user-defined vehicles, safety Level 2+ (L2+) automated driving, and the evolving vehicle architectures […]
Embedded virtualization hypervisor runs on RH850/U2A MCUs
Green Hills Software announced the release of µ-visor, its safe and secure embedded virtualization hypervisor, for the Renesas RH850/U2A microcontroller (MCU). Designed to support the emerging automotive cybersecurity requirements of ISO/SAE 21434 and UNECE WP.29 and to meet ISO 26262 ASIL D functional safety, µ-visor for MCUs expands Green Hills leadership in safe and secure virtualization […]
J-Link Remote Servers speed embedded system debugging
SEGGER announces that it now operates a worldwide network of J-Link Remote Servers, enabling a user to debug target systems from anywhere in the world at even higher speeds than before. The J-Link Remote Servers are available to every J-Link user at no cost. While using the closest server significantly increases communication speed, customers still […]
Utilities speed software development on complex MCU cores
Renesas Electronics Corporation announced the release of IP Utilities – a new series of solutions aimed at simplifying the development of devices incorporating Renesas intellectual property (IP). The new IP Utilities include application packages and evaluation kits, as well as expanding Renesas’ growing portfolio of leading-edge IP licenses. With the emergence of CPUs based on […]
New IDE linker program shrinks executable code by 15%
SEGGER’s Embedded Studio for RISC-V now comes with the SEGGER Linker in addition to the GNU linker. The SEGGER Linker has been developed from the ground up to create executables for Embedded Systems. For RISC-V, it shrinks the size of the resulting programs by up to 15%, shortens link time, delivers a detailed map file, […]
RISC-V is growing and offers stability, scalability and security
RISC-V is growing rapidly. Semico Research has projected that 62.4 billion RISC-V CPU cores will be sold in 2025. While that’s only about 6% of the overall CPU core market, RISC-V is an emerging technology that most designers should follow and become increasingly familiar with. RISC-V is becoming more commercially attractive as a result of […]
Development tools help meet EN 303 645, consumer IoT security standards
Secure Thingz, an IAR Systems Group company, presents updated versions of its security development tools Embedded Trust and C-Trust. These new versions support next-generation Secure Install technologies intended to prevent malware throughout device lifecycles, enhance the protection of Intellectual Property (IP) and inhibit the cloning and counterfeiting of embedded applications. These new capabilities will also […]